Executive Summary
1.1 Purpose of the White Paper
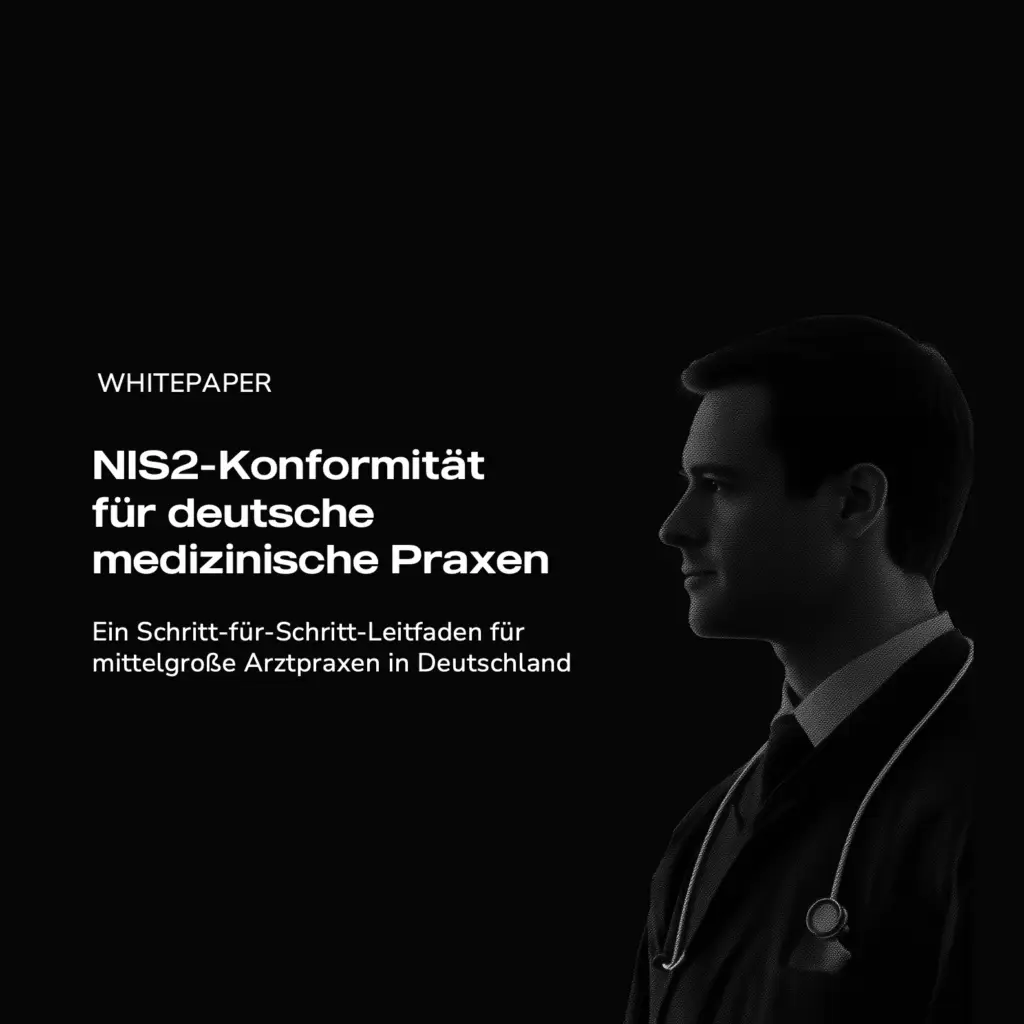
The NIS2 Directive promises to reshape cybersecurity standards across the European Union, directly impacting medium-to-large medical practices in Germany—particularly those with more than 50 employees or over €10 million in annual revenue. Concurrently, cyber threats against healthcare providers continue to escalate, with ransomware attacks and data breaches causing not only financial harm but also life-threatening care disruptions.
This white paper offers straightforward, actionable guidance to help practice owners, partners, and administrators understand their obligations under NIS2 and implement robust cybersecurity measures. Beyond merely outlining regulations, it emphasizes practical steps for safeguarding critical systems and patient data, including:
- A checklist for NIS2 readiness, covering governance, risk assessment, policies, staff training, and incident response.
- A case study, “Bright Smiles Orthodontics,” demonstrating how a mid-sized practice addressed key compliance challenges.
- Insights into the role of Fractional CISO services in filling vital security leadership gaps—at a fraction of the cost of a full-time hire.
1.2 Key Takeaways
- Cybersecurity = Care Quality: A single, well-placed cyberattack can delay treatments, compromise patient outcomes, and erode trust in your practice. By investing in robust security protocols, you’re also safeguarding the core of your clinical mission.
- Benefits of Compliance: Going beyond legal obligation, proactive cybersecurity protects your reputation, prevents costly downtime, and above all, ensures continuity of patient care.
- Scope & Timelines: If your practice meets NIS2 criteria, it’s essential to initiate cybersecurity improvements right away (see Chapter 8 for the most recent timeline updates).
- Compliance is Within Reach: This paper provides the practical steps you need—an actionable checklist, real-world examples, and clear explanations—so you can begin fortifying your practice against threats immediately.
Healthcare Under Siege: The Evolving Cyber Threat Landscape
Healthcare organizations across Europe—and indeed, worldwide—are under siege from cybercriminals. From phishing scams that compromise patient data to full-scale ransomware assaults that cripple core clinical services, the stakes could not be higher. This chapter illustrates how these threats directly impact patient care and underscores why the newly expanded NIS2 Directive isn’t just a legal formality—it’s a protective shield for both patients and practitioners.
2.1 Attacks That Disrupted Lives, Not Just Systems
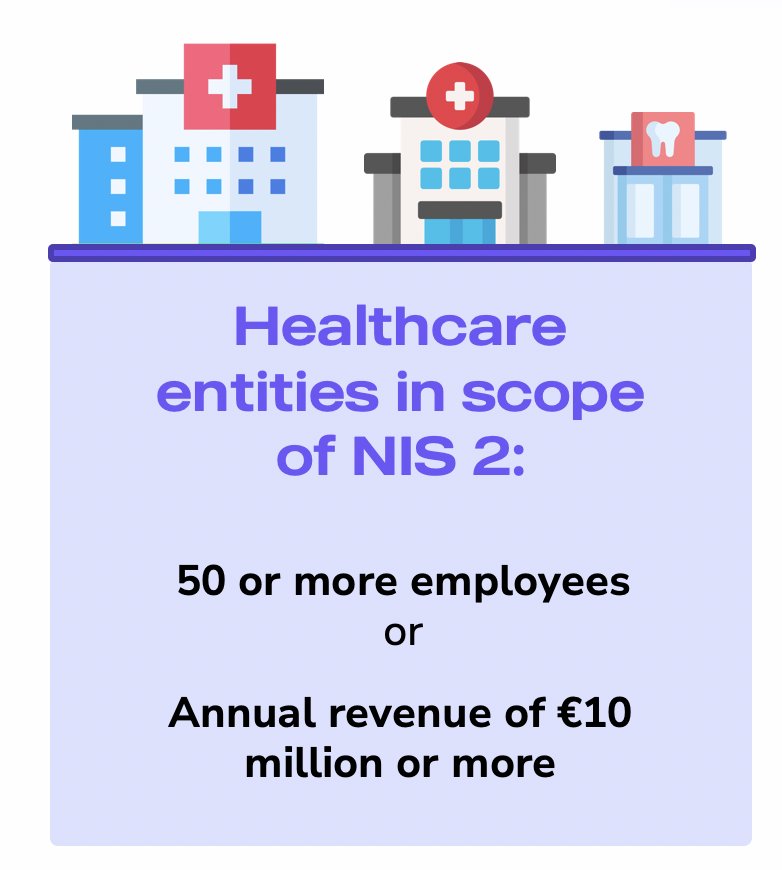
One of the most alarming recent examples comes from June 2024, when a ransomware attack devastated Synnovis Lab Services, a pathology provider for London’s NHS hospitals. This breach was not an isolated “IT problem”—it rippled directly into patient care. With critical lab systems offline, hospitals had to postpone over 10,000 outpatient appointments and 1,700 surgeries, delaying essential medical treatments and procedures. In the immediate aftermath, lab tests and diagnostic services operated at roughly 10% capacity, creating significant backlogs and confusion for both medical staff and patients .
A subsequent review attributed at least 498 patient safety incidents to this attack, including 119 incidents of patient harm and 5 cases of moderate harm where individuals suffered notable health complications. Doctors on the ground described the situation as “chaotic,” explaining that critical lab results were unavailable, and serious conditions went unmonitored for days, if not weeks. For healthcare providers in Germany—large hospitals and smaller specialty clinics alike—this scenario underscores a harsh reality: a single cyber incident can disrupt core clinical functions and, in turn, endanger patient lives.
2.2 The Clinical Costs of Cyberattacks
Sadly, the Synnovis incident is far from unique. Multiple studies show that cyberattacks on healthcare often translate into worse patient outcomes. In a 2022 Ponemon Institute survey, 57% of healthcare organizations reported direct negative impacts on care from cyber incidents, with over 20% noting an increase in mortality rates following major attacks. Another study from Proofpoint found that among ransomware-hit hospitals, 67% experienced significant care disruption (delayed or canceled treatments), while 24% observed higher mortality rates in the wake of these breaches.
Such statistics underscore a new reality: cybersecurity is about far more than safeguarding data; it’s about ensuring clinical continuity and patient well-being. For physicians and clinic owners, adequate security measures have become as vital as sterile equipment or sound infection control protocols.
2.3 The Underreported Frequency of Attacks
While headline-grabbing attacks tend to focus on large hospital networks, the vast majority of incidents—upwards of 89% of healthcare organizations—suffer at least one cyberattack per year. Crucially, many breaches go unreported, leaving a gap in the public data. Ransomware remains especially prevalent because healthcare providers, under duress to restore essential services, are more inclined to pay quickly. In this environment, mid-sized clinics should not assume they are overlooked by criminals; in fact, their often-limited cybersecurity infrastructure makes them even more alluring targets.
2.4 Why Medium-Sized Practices Are a Prime Target
It can be tempting to think cybercrime affects only large hospitals, but practices with 50 to 250 employees also face significant risks. They often rely on digital systems for scheduling, diagnostics, billing, and medical records, yet might not have robust, in-house cybersecurity expertise or resources. Even a brief shutdown of these services can disrupt patient appointments, slow down diagnoses, and create a backlog of urgent tasks.
In a digitally interconnected world, one compromised practice can also serve as an entry point for attackers to move laterally into affiliated hospitals or specialized service providers. This is exactly why NIS2 expands its scope to include these mid-sized healthcare entities: any weak link in the chain can place the broader network at risk . By setting a clear set of cybersecurity standards for even “smaller” practices, NIS2 aims to raise the security baseline across the entire healthcare ecosystem, preventing attackers from exploiting the perceived gaps in less-resourced settings.
2.5 BSI Findings: A Look into German Medical Practices
In Germany, the Bundesamt für Sicherheit in der Informationstechnik (BSI) has documented glaring vulnerabilities through various studies and audits:
- SiRiPrax Study: In a nationwide survey involving 1,600 medical practices, only one-third of respondents said they had fully implemented all the protective measures required under § 75b SGB V (the IT-Security Guidelines). In addition, 10% of these practices had already experienced at least one IT security incident .
- CyberPraxMed Project: The BSI uncovered critical security shortcomings such as insufficient malware protection, poor patch management, and a complete lack of backups in some cases. Notably, it found that the Konnektor (used to connect practices to the Telematics Infrastructure) often operated in parallel with a standard router, undermining its intended security function. Moreover, none of the surveyed practices employed full disk encryption to protect sensitive patient data .
These findings illustrate that even established practices fall short of basic cybersecurity hygiene, leaving them vulnerable to attacks that can disrupt operations and compromise patient data. With the expansion of NIS2, medium-sized clinics in Germany can no longer afford to overlook these gaps. By proactively addressing known weaknesses—such as robust patching, segregated network configurations, secure backups, and proper data encryption—practices not only move toward compliance but also safeguard patient trust and care quality.
NIS2 in German Healthcare: Raising the Cybersecurity Bar
3.1 From NIS to NIS2: Why the Directive Needed an Upgrade
Evolution of the Original NIS Directive
Adopted in 2016, the Network and Information Security (NIS) Directive was the EU’s first attempt at tackling cybersecurity across critical sectors, including healthcare. Operators were required to implement basic security measures and report incidents, but rapidly escalating threats soon exposed significant gaps.
The Push towards NIS2
In response to these gaps and the rising tide of cyberattacks, the EU introduced NIS2. Its key objectives are:
- Expanding the Scope: More sectors and entities, including medium-sized healthcare practices, now fall under mandatory requirements.
- Harmonizing Enforcement: Stronger, more consistent rules across all member states to prevent patchwork implementation.
- Strengthening Provisions: Tighter reporting timelines and clear accountability—particularly for senior leadership—ensure that cybersecurity is taken seriously at every level of an organization.
A Pan-EU Goal: Resilient Critical Services
NIS2 is built on the principle that an attack on one healthcare provider can have cascading effects across an entire national and international network. By enforcing minimum standards for risk management, incident response, and governance, NIS2 intends to keep essential services running even under cyber duress—especially crucial in an interconnected sector like healthcare .
3.2 Germany’s Adoption: What It Means for Medium-Sized Practices
Key Oversight Bodies: BSI and KBV
In Germany, cybersecurity efforts are spearheaded by the Bundesamt für Sicherheit in der Informationstechnik (BSI), which sets guidelines, conducts audits, and offers advisories on best practices. The Kassenärztliche Bundesvereinigung (KBV) oversees medical service providers in outpatient care, setting and enforcing IT security guidelines under § 75b SGB V—primarily affecting smaller practices with fewer than 50 employees.
Where the BSI often provides technical frameworks and standards (e.g., IT-Grundschutz catalogs), the KBV ensures these frameworks are appropriately adapted and enforced in outpatient care settings. Together, these organizations will be integral in interpreting and implementing NIS2 requirements for German healthcare providers, from large hospital networks down to mid-sized practices and specialized clinics.
Where Practices Fit: Small, Medium, NIS2 or Critical (KRITIS)
The KBV categorizes medical practices by employee count into “Praxis” (1–5 employees), “Mittlere Praxis” (6–20), and “Großpraxis” (> 20). However, these do not map directly to NIS2 or KRITIS thresholds:
Practices with Fewer Than 50 Employees
- Typically follow KBV’s IT Security Guidelines.
- Remain below NIS2’s 50-employee threshold unless they exceed NIS2’s €10 million annual revenue criterion.
NIS2 Coverage (“Wichtige Einrichtungen,” “Besonders wichtige Einrichtungen”)
- Kicks in at ≥50 employees or ≥€10 million annual revenue, whichever criterion is met.
- Many so-called “Großpraxen” may still be below NIS2 thresholds if they fall short on revenue. Conversely, a “Mittlere Praxis” might meet the revenue criterion if it’s highly profitable.
KRITIS Operators
- Very large healthcare providers (e.g., major hospitals) that surpass specific inpatient or capacity limits are classified as KRITIS.
- This classification imposes even stricter security requirements beyond NIS2.
Below is a quick reference chart illustrating how KBV-regulated practices, NIS2-covered entities (wE / bwE), and KRITIS operators align in terms of staffing and financial thresholds:
Classification of medical practice in accordance with German cybersecurity regulations
While NIS2 has been adopted at the EU level, Germany’s draft NIS-2 Implementation and Cybersecurity Strengthening Act (NIS2UmsuCG) translates the directive into national law by distinguishing between:
1. Wichtige Einrichtungen (wE)
Typically organizations with 50–249 employees, annual revenue ≥€10 million and <€50 million, or a balance sheet total ≥€10 million and <€43 million.
2. Besonders wichtige Einrichtungen (bwE)
Larger entities with ≥250 employees, annual revenue ≥€50 million, or balance sheet total ≥€43 million.
3. Kritische Anlagen (KRITIS)
Entities meeting specific “critical infrastructure” thresholds, subject to even stricter obligations.
It is estimated that around 30,000 organizations will be impacted across eleven key sectors. For mid-sized healthcare practices—often falling under the wE category—this marks a significant shift: they can no longer assume they’re “too small” for mandated cybersecurity requirements.
Current Status and Timelines
Germany is finalizing its NIS2 transposition, and legislative delays have pushed the projected enforcement date into early 2025 (see Chapter 8 for detailed timelines). Despite these delays, the rising tide of ransomware attacks and data breaches underscores the urgency for clinics to fortify their defenses now—cybercriminals won’t wait for the law to take effect.
3.3 Connecting Threats to NIS2 Measures
As highlighted in the previous section, mid-sized healthcare organizations face many of the same risks as larger hospitals. NIS2 directly addresses these vulnerabilities by:
- Mandating Security Upgrades: Incident response plans, risk assessments, and governance frameworks become non-negotiable.
- Stipulating Strict Reporting: Faster and more transparent reporting of breaches helps contain attacks before they escalate.
- Holding Leadership Accountable: Executive teams can no longer delegate cybersecurity as a purely technical concern.
For German medical practices, the message is clear: meeting NIS2 requirements is not about ticking a regulatory box; it’s about safeguarding clinical operations, protecting patient data, and maintaining trust in an increasingly digitized healthcare environment.
New Obligations Under NIS2: What Medium-Sized Clinics Need to Know
The NIS2 Directive imposes clear and stringent requirements on healthcare entities in the European Union—particularly those with 50+ employees or annual revenues exceeding €10 million. For medical practices, this is more than a bureaucratic exercise: robust cybersecurity measures safeguard patient data, ensure continuity of care, and protect the organization from potentially crippling fines. This section outlines the core obligations, the penalties for failing to meet them, and the critical link between compliance and patient well-being .
4.1 Key Compliance Requirements
4.1.1 Core Technical and Organizational Mandates
Security Policies & Risk Assessments
Conduct regular audits of your IT landscape (patient record systems, diagnostic tools, scheduling software) to identify vulnerabilities. These assessments form the foundation of comprehensive security policies governing everything from password rules to network segmentation.
Incident Detection & Response
Maintain real-time monitoring for suspicious activity and have a clear plan to contain breaches. Define roles and responsibilities in advance—who reports the incident, who coordinates with authorities—so critical decisions aren’t delayed in a crisis.
Business Continuity & Disaster Recovery
NIS2 requires that healthcare services continue even during a cyberattack. Frequent data backups, ideally stored offline, and emergency operational workflows (e.g., paper-based processes) minimize downtime, ensuring patients still receive care.
Securing the Supply Chain
Clinics rely heavily on external vendors for software, cloud EHR solutions, and lab services. Under NIS2, you must vet and continuously monitor each partner’s cybersecurity practices to avoid letting attackers into your network via a third-party vulnerability.
Access Control & Data Protection
Implement multi-factor authentication (MFA) and regularly review who can access sensitive systems. Data encryption—both at rest and in transit—provides an added layer of protection against unauthorized disclosure.
Secure Development & Patching
Whether you build or buy software, timely patching is non-negotiable. New vulnerabilities emerge daily, and unpatched systems are an open invitation for cybercriminals.
Continuous Evaluation & Improvement
Ongoing security checks—such as vulnerability scans and penetration tests—are now a core expectation. Regular auditing ensures that measures remain effective against an ever-evolving threat landscape.
4.1.2 Reporting Duties and Accountability
Fast-Track Reporting
NIS2 mandates that significant incidents be reported to the Bundesamt für Sicherheit in der Informationstechnik (BSI) within 24 hours. A follow-up report is typically due within 72 hours, with final updates as the incident unfolds.
Leadership in the Spotlight
C-level executives, managing physicians, and practice owners can be held personally liable if they ignore known cyber risks. By making cybersecurity a board-level priority, NIS2 aims to prevent it from becoming just an afterthought in the budget.
4.2 The High Cost of Non-Compliance
Penalties for Non-Compliance with NIS 2
Non-compliance can lead to the following penalties and consequences:
- Financial Fines: Penalties can reach up to €10 million or 2% of annual turnover, whichever is higher. For mid-sized clinics operating on tighter margins, such fines could threaten long-term viability.
- Personal Liability for Management: Leaders may face legal consequences if gross negligence is found. Already, healthcare boards in several EU countries are treating cybersecurity with the same urgency as patient safety and malpractice risks.
- Reputational Damage: Healthcare operates on trust; patients expect their information and appointments to be secure. A data breach, leaked records, or canceled procedures can tarnish a practice’s reputation long after the incident is resolved.
- Operational Consequences: In severe cases, regulators can halt certain operations until security issues are fixed. Insurance claims may also be denied if negligence is proven, and civil lawsuits can follow from patients affected by disruptions or data exposure.
4.3 Why It All Matters: Patient Safety and Care Continuity
While financial and legal liabilities often take center stage, the most critical dimension is patient well-being:
- Direct Clinical Impact: Ransomware attacks that lock or corrupt patient data, lab results, or treatment schedules can lead to delayed diagnoses, canceled surgeries, and potential life-threatening complications.
- Patient Trust and Confidence: A strong security stance can be a market differentiator, reassuring patients that their private health data is in capable hands. Conversely, a major breach undermines confidence and can send patients elsewhere.
- Avoiding Catastrophic Scenarios: As demonstrated by the Synnovis Lab Services attack, even a single breach can ripple across labs, clinics, and hospitals, disrupting thousands of appointments. NIS2’s emphasis on incident response and disaster recovery is designed to mitigate precisely these kinds of large-scale failures.
By embracing NIS2 obligations, German medical practices safeguard not only their bottom line but also the core mission of healthcare: providing timely, effective care without compromising patient trust. In the next sections, we’ll dive deeper into practical cybersecurity measures to meet these demands and discuss how Fractional CISO services can help organizations navigate NIS2 compliance efficiently and sustainably.
Practical Cybersecurity Measures & Checklist
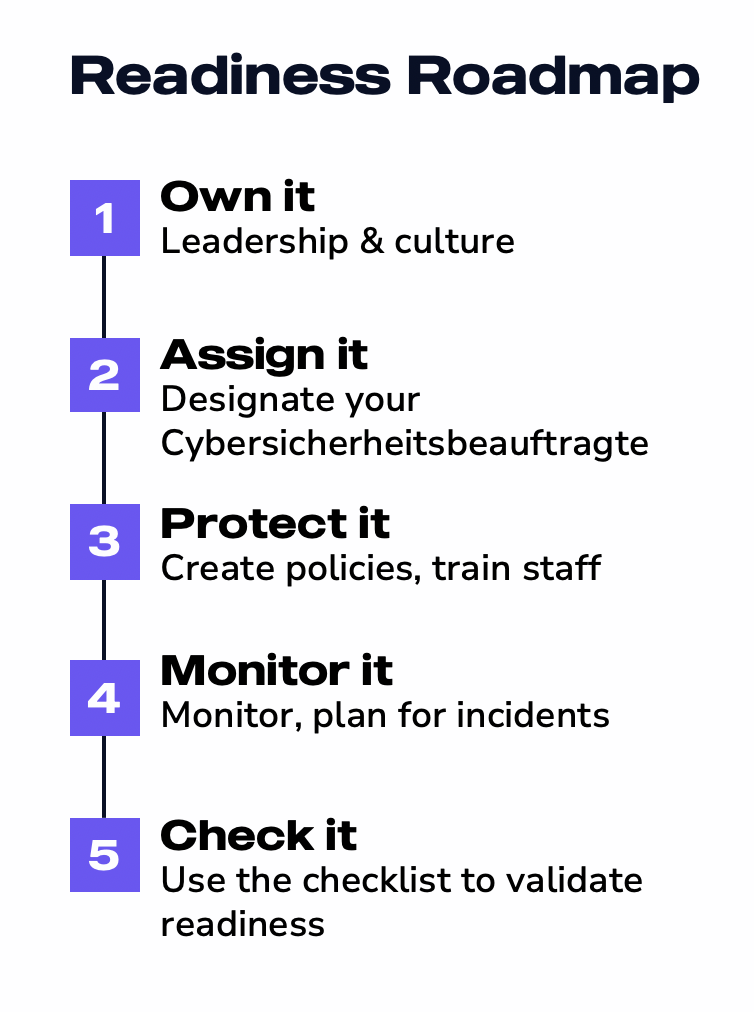
NIS2 can feel overwhelming for busy medical practice owners, but compliance ultimately boils down to systematic planning, clear leadership, and ongoing vigilance. It’s not just an “IT problem” for a technician to solve—it’s a strategic priority that requires visible commitment from top management and a strong culture of security across the entire organization.
In the following sections, we’ll start by focusing on the human and organizational elements of cybersecurity—how leadership, governance, and an appointed Cyber-Sicherheitsbeauftragte shape the clinic’s overall readiness. Only after establishing this crucial foundation will we delve into specific measures such as risk assessment, policy creation, monitoring, and incident response.
5.1 Leadership, Culture, and Governance
Cybersecurity in healthcare is, first and foremost, a leadership challenge. Under NIS2, practice owners and managing physicians carry legal and ethical responsibility for ensuring patient data is protected and that clinical operations can withstand digital threats. This section explains how top-level commitment and a security-focused culture can make or break your practice’s defense against cyberattacks.
5.1.1 Setting the Tone from the Top
Owner-Level Accountability
NIS2 places a heightened emphasis on personal liability for gross negligence. If leadership ignores known risks or fails to dedicate resources to basic safeguards, the consequences can include significant fines and even individual legal repercussions. Therefore, the security conversation must begin in the boardroom or partnership meetings, not in the IT department alone.
Aligning with BSI and KBV Expectations
In Germany, the Bundesamt für Sicherheit in der Informationstechnik (BSI) and the Kassenärztliche Bundesvereinigung (KBV) provide guidelines and oversight for healthcare cybersecurity. Practice owners need to be aware of how these bodies classify their clinics (as an “essential” or “important” entity under NIS2) and what specific responsibilities arise as a result. By proactively engaging with these requirements, you demonstrate a commitment to security that resonates throughout the organization.
5.1.2 Creating a Security-First Culture
Why Culture Matters
Even the most advanced technical controls can be undermined if staff are lax about passwords, click on phishing links, or skip software updates. Building a security-first culture means ensuring everyone—from receptionists to physicians—understands their role in protecting patient data.
Communicating the ‘Why’
Link cybersecurity to patient well-being and trust. Emphasize that safeguarding systems is not a compliance box-tick but a core element of delivering quality care. When employees see how a ransomware attack can disrupt surgeries or lab results, they’re more likely to follow security best practices.
Practical Steps to Build Engagement
- Hold regular briefings at staff meetings to share updates on new threats.
- Celebrate “security wins,” like successfully detecting a phishing attempt.
- Encourage a “report-it-early” mentality where staff can flag anomalies without fear of blame.
5.1.3 Assigning Responsibility: The Role of a Cybersicherheitsbeauftragte
Why You Need a Security Lead
Under NIS2, medium-sized medical practices are now expected to have a designated individual (or team) responsible for overseeing cybersecurity initiatives. This Cybersiicherheitsbeauftragte acts as the linchpin for all security-related decisions—coordinating everything from risk assessments to incident response.
Key Responsibilities
- Risk Oversight: Collaborate with IT providers to evaluate threats and recommend safeguards.
- Policy Enforcement: Ensure guidelines (e.g., access control, BYOD rules) are documented, communicated, and followed.
- Incident Management: Serve as the central point of contact for breach detection, containment, and reporting to the BSI within mandated timelines.
- Ongoing Training: Organize staff education sessions on phishing, social engineering, and other relevant topics.
- Reporting Lines and Decision-Making
The Cybersicherheitsbeauftragte should report directly to practice owners or managing physicians, providing regular updates on emerging risks and the effectiveness of current measures. This arrangement guarantees that leadership remains fully informed and can quickly allocate resources when issues arise.
5.2 Risk Assessment Essentials
Once leadership and governance are in place, the next critical step is to identify where your practice is most vulnerable. A formal risk assessment is the cornerstone of any cybersecurity program, ensuring that resources are allocated effectively and that you have a clear understanding of the threats your organization faces.
5.2.1 Why Risk Assessments Matter
A well-structured risk assessment provides a clear roadmap for security investments and ensures that your practice meets NIS2 compliance requirements. It acts as:
- Foundation for Decision-Making: A comprehensive risk assessment guides you on where to invest time, money, and training. It reveals which systems, devices, and workflows demand the most immediate attention—be it patient record databases, lab diagnostic equipment, or front-desk computers.
- Compliance Driver: Under NIS2, demonstrating proactive and ongoing risk assessment efforts is essential for compliance. Regulators and auditors expect to see documentation that your practice regularly evaluates and addresses new threats.
- Continuous Process: Cyber threats evolve rapidly; a single risk assessment is not enough. By scheduling assessments at least annually—or whenever major IT changes occur—you ensure that new vulnerabilities are caught before attackers exploit them.
5.2.2 Identifying Critical Systems and Data
Not all systems carry the same level of risk. Some are mission-critical, containing sensitive patient information or supporting essential clinical workflows. Identifying these high-value assets ensures that protection efforts are prioritized where they matter most.
1. Patient Records & EMRs
Electronic medical records, billing data, and scheduling platforms are high-value targets for both ransomware and data theft. Consider them your “crown jewels” and assign protective measures accordingly.
2. Medical Devices & IoT
From imaging machines to diagnostic equipment, many devices run on older or proprietary operating systems that are often unpatched. These can become weak links in your security chain.
3. Administrative Platforms
Email servers, staff communication tools, and shared document repositories may not store patient data directly, but they remain prime entry points for phishing and malware attacks.
5.2.3 Evaluating Vulnerabilities and Threat Scenarios
With critical systems identified, the next step is to assess how they might be compromised. This involves mapping out common attack vectors, recognizing human error risks, and evaluating potential weaknesses in third-party service providers.
1. Common Attack Vectors
- Ransomware: Encrypts files, leading to severe service disruption.
- Phishing: Targets human error; a single click can compromise your network.
- Exploits & Unpatched Systems: Attackers seek known software flaws in outdated devices or operating systems.
2. Human Factors
Your staff’s daily habits—clicking links, reusing weak passwords, or neglecting routine updates—can significantly increase risk. Include human errors or insider threats in every risk assessment.
3. Supply Chain Risks
Verify that third-party software vendors, cloud service providers, and IT consultants uphold strict security standards. A vulnerability in one vendor’s system can compromise your entire practice.
5.2.4 Practical Steps for Conducting a Risk Assessment
A risk assessment should be structured and repeatable, ensuring that no key assets are overlooked. The following step-by-step approach helps organize and document findings so that remediation efforts can be effectively planned and executed.
1. Inventory All Assets
List every device, application, and data repository you rely on, from front-desk computers and staff laptops to specialized imaging equipment and cloud platforms.
2. Classify Data Sensitivity
Prioritize assets based on the type of information stored or accessed. Patient-identifiable data and medical records typically require the highest level of protection.
3, Identify Threats & Vulnerabilities
Work with your Cyber-Sicherheitsbeauftragte and IT team to map potential attack pathways—phishing, malware, unsecured Wi-Fi, weak passwords, etc.
4. Estimate Likelihood & Impact
Assign a likelihood score (e.g., low, medium, high) and an impact rating (e.g., minimal operational disruption vs. complete shutdown). This helps in prioritizing remediation efforts.
5. Develop a Remediation Plan
- Short-Term Fixes: Quick wins such as enabling multi-factor authentication, updating antivirus software, and patching critical systems.
- Long-Term Strategies: Projects that require investment or staff training, like upgrading legacy devices or rolling out new security policies.
6. Document and Communicate
Maintain a written record of findings and share them with practice owners, the Cyber-Sicherheitsbeauftragte, and relevant staff. This documentation also serves as evidence of due diligence if audited.
5.2.5 Turning Insights into Action
A risk assessment isn’t just a report—it’s a roadmap for strengthening your security posture. Revisit the results in regular leadership meetings to track progress and ensure accountability. If new software is introduced or the practice expands its services, update the assessment to reflect added risks.
Key Takeaway: A structured, well-documented risk assessment is the bedrock of effective cybersecurity under NIS2. By shining a spotlight on your practice’s unique vulnerabilities, you can make informed, strategic decisions that protect patient care and data—while satisfying the directive’s requirements for ongoing risk management.
5.3 Policies, Training, and Organizational Measures
With leadership in place and key risks identified, the next logical step is to codify and operationalize your security strategy. Policies, training programs, and clear lines of accountability ensure that good intentions become day-to-day practices—ultimately protecting both patient data and clinical operations.
5.3.1 Building Effective Policies
1. Access Control & Authentication
- Least Privilege: Limit each employee’s access rights to the minimum necessary for their role.
- Strong Passwords & MFA: Encourage complex passwords, regular password changes, and multi-factor authentication (MFA), particularly for administrative or remote access.
- BYOD Guidelines: If staff use personal devices, clearly define acceptable use and security standards (e.g., mandatory mobile device management, remote-wipe capabilities).
2. Incident Response & Business Continuity
- Playbooks: Develop clear, step-by-step instructions for handling various attack scenarios (e.g., ransomware, phishing, data breaches).
- Escalation Path: Specify who notifies the BSI (in Germany) and within what timeframe, as well as who handles communications with staff, patients, and media.
- Contingency Plans: Detail how patient care will continue (e.g., reverting to paper-based processes) if digital systems fail.
3. Data Protection & Record-Keeping
- Encryption: Mandate data encryption both at rest and in transit, especially for patient records and lab results.
- Retention Policies: Define how long data is stored, and under what conditions it can be purged or archived.
- Audit Logs: Keep detailed logs of data access and modifications to quickly identify suspicious activity.
4. Supplier and Vendor Management
- Security Clauses: Include explicit cybersecurity requirements in contracts with third-party vendors (e.g., cloud EHR systems, billing providers).
- Ongoing Due Diligence: Periodically review vendors’ security certifications, incident history, and patching protocols.
Tip: Keep these policies organized and accessible—staff can’t follow rules they don’t know or can’t find. Regularly update them to reflect changes in technology, regulatory requirements, or emerging threats.
5.3.2 Staff Training and Awareness
1. Multi-Level Engagement
- Front Desk to C-Suite: Everyone with network access or patient-facing responsibilities should receive tailored security training.
- Annual Refresher Courses: Reinforce key topics like phishing prevention, secure data handling, and incident reporting.
2. Phishing and Social Engineering Drills
- Simulated Attacks: Send fake phishing emails to staff at random intervals to measure and improve response rates.
- Feedback Loop: Provide immediate feedback on whether an email was a test and what red flags staff should have noticed.
3. Encourage a “Speak Up” Culture
- Reporting Without Fear: Promote an environment where employees can report suspicious emails, system anomalies, or policy gaps without fear of blame.
- Continuous Improvement: Regularly gather staff feedback on the usability of policies, training materials, and reporting channels.
4. Documentation and Compliance
- Training Records: Maintain a log of who was trained, on what topics, and when. In case of an audit or breach investigation, this documentation demonstrates compliance efforts.
Key Point: Even the best technology fails if people click the wrong links or ignore essential updates. Ongoing staff education is crucial for translating policy into practice.
5.3.3 Governance and Accountability
1. Designated Security Lead
- Cyber-Sicherheitsbeauftragte: Ensure your clinic has a single point of contact responsible for overseeing policy enforcement, training schedules, and incident management.
- Direct Reporting Line: This individual should provide periodic updates to senior leadership, keeping them informed of new threats, policy revisions, and compliance timelines.
2. Regular Policy Reviews
- At Least Annually: Schedule a formal policy review session in tandem with your annual risk assessment.
- Ad Hoc Updates: Major IT changes—like adopting a new electronic health record (EHR) system or integrating an external laboratory service—should trigger an immediate policy review.
3. Leadership Oversight
- Owner/Partner Engagement: Practice owners must take an active role in approving budget allocations for security and verifying that policy changes align with patient care objectives.
- Audit & Compliance: Under NIS2, owners may be personally liable for ignoring known cyber risks. Regularly documented oversight can help mitigate liability.
5.3.4 From Policy to Practice
Effective cybersecurity policies and well-trained staff form the backbone of NIS2 compliance. However, policies alone won’t secure your clinic if they aren’t consistently applied. Frequent communication, ongoing training, and visible leadership support will help transform these guidelines into a lived culture of security.
Key Takeaway: By formalizing policies, training your team, and establishing clear lines of accountability, your practice transitions from knowing its risks to actively managing them. This proactive stance is crucial for maintaining trust with patients and meeting NIS2 obligations.
5.4 Monitoring & Incident Response
Even the best-laid security plans can’t guarantee zero breaches. Cyber threats continue to evolve, and healthcare organizations remain high-value targets. To fulfill NIS2 obligations—and to safeguard patient well-being—your practice must be equipped to detect threats early and respond decisively when incidents occur.
5.4.1 Why Continuous Monitoring Matters
- Early Detection of Threats: A suspicious file transfer, an atypical login at odd hours, or a sudden spike in network traffic can be the first sign of a breach. Continuous monitoring helps spot these warning signs before they escalate.
- Regulatory Compliance: Under NIS2, healthcare entities are required to have mechanisms that detect and report significant incidents promptly. Logging and monitoring tools provide evidence of due diligence when auditors come knocking.
- Preserving Patient Safety: The faster you detect an anomaly, the quicker you can isolate compromised systems and prevent a full-scale shutdown of clinical services.
Key Tools & Practices
- SIEM (Security Information and Event Management) systems to centralize and analyze log data from various sources.
- Vulnerability Scanning at regular intervals to catch unpatched software or device misconfigurations.
- Network Segmentation to limit the spread of malware or unauthorized access if one segment is compromised.
5.4.2 Crafting a Robust Incident Response Framework
1. Preparation
- Incident Response Playbook: Document clear, step-by-step protocols for common attack scenarios (ransomware, phishing, data exfiltration).
- Predefined Roles: Assign responsibilities (e.g., who contacts the BSI, who leads internal communication, who manages patient notifications if needed).
2. Detection & Analysis
- Alert Mechanisms: Ensure your monitoring tools are configured to send real-time alerts to both the Cyber-Sicherheitsbeauftragte and relevant IT personnel.
- Initial Assessment: Quickly determine the scope and nature of the incident—what systems are affected, what data might be at risk?
3. Containment & Eradication
- Isolate Systems: Quarantine infected devices or networks to prevent lateral movement by attackers.
- Remove Threats: Work with IT partners or incident response experts to eliminate malware or unauthorized access.
- System Hardening: Patch vulnerabilities, reset compromised passwords, and strengthen security controls to avoid repeat incidents.
4. Recovery & Restoration
- Backups: If your offline backups are intact, restore systems to a clean state.
- Data Validation: Verify data integrity before resuming normal operations; patient records must be accurate for safe care delivery.
5. Post-Incident Review
- Root Cause Analysis: Determine how the breach occurred—human error, unpatched software, vendor misconfiguration, etc.
- Action Items: Update policies, training modules, and infrastructure to address gaps identified during the incident.
5.4.3 Communication & Reporting Under NIS2
1. 24-Hour Reporting
If an incident meets the “significant” threshold—disrupting critical services or causing substantial financial damage—you must notify the Bundesamt für Sicherheit in der Informationstechnik (BSI) within 24 hours of detection.
2. Ongoing Updates
A more detailed report is typically due within 72 hours, followed by final updates once the incident is fully contained. Transparency ensures that authorities can coordinate broader defense measures if the attack is widespread.
3. Internal Communication
- Staff Alerts: Let personnel know when systems are compromised, providing clear instructions (e.g., do not log in to certain networks).
- Patient Notifications: In cases where patient data may be at risk, timely communication is not just a legal requirement but also a cornerstone of maintaining trust.
4. Media and Public Relations
Cyber incidents can attract media attention. Develop a concise, factual statement that explains the situation without disclosing sensitive details or jeopardizing ongoing investigations.
5.4.4 Testing Your Response Readiness
- Tabletop Exercises & Simulations: Periodically run mock incidents—such as a hypothetical ransomware outbreak—to evaluate how quickly staff recognize and contain threats. These drills also reveal any confusion about roles or escalation paths.
- After-Action Reports: Document lessons learned from each exercise or real incident. Update policies and training programs to address any newly discovered vulnerabilities or communication gaps.
- Continuous Improvement Loop: Successful incident response is a cycle of preparation, testing, response, and refinement. A single drill or policy update is never enough—stay vigilant and adapt to emerging threats.
5.4.5 Key Takeaways for Busy Practice Owners
- Preparedness Is Paramount: Have a well-drilled plan in place before an attack happens—there’s no time to figure it out during a crisis.
- Early Alerts Save Lives: Rapid detection and containment can mean the difference between a minor disruption and a full-scale shutdown affecting patient care.
- Clear Reporting Lines: Know exactly who alerts the BSI within 24 hours, and who communicates internally and externally.
- Documentation Is Vital: Thorough records of every action taken during an incident help with both legal compliance and refining future response strategies.
In the final subsection of this chapter, we’ll provide a quick checklist that consolidates the essentials—helping you gauge at a glance whether your practice has covered the fundamental bases of NIS2-readiness.
5.5 Checklist for NIS2-Readiness
For non-technical leaders seeking immediate clarity, here’s a concise checklist to gauge whether you’re covering the basics:
- Leadership & Governance
Have you assigned a clear cybersecurity lead (internal or external)?
Do senior decision-makers review security risks at least quarterly?
Is there a documented incident response plan with BSI reporting guidelines?
- Risk Management & Policies
Risk Assessment: Performed at least once a year?
Policies: Formalized (access control, device usage, remote work, etc.) and reviewed regularly?
Incident Response Plan: Updated, practiced, and accessible to all relevant staff?
- Technical Safeguards
Access Controls: MFA enabled for administrative accounts and remote access?
Encryption: All patient data encrypted at rest and in transit?
Backups: Regularly tested, stored securely offline, and updated?
Patching: Are software and hardware consistently updated with latest security fixes?
- Monitoring & Detection
Logging: Do you log key events across servers, devices, and critical applications?
Alerts: Is there a system to quickly notify IT/security staff of suspicious activity?
Vulnerability Scans: Scheduled scans (monthly or quarterly) to catch potential exploits?
- Training & Culture
Staff Training: Provided at least annually on cybersecurity best practices?
Phishing Drills: Occasional tests to see if staff can spot malicious emails?
Reporting Culture: Staff encouraged to report incidents or anomalies without fear of retribution?
By systematically working through this checklist, medical practice owners can pinpoint gaps and prioritize next steps, ensuring that their security programs align with NIS2 requirements.
This combination of risk assessments, policies, technical safeguards, ongoing monitoring, and staff training forms the backbone of any healthcare cybersecurity strategy. The key is consistent execution and continuous improvement, not just a one-time compliance effort. In the following sections, we will explore how outsourcing key cybersecurity roles—like engaging a Fractional CISO—can help medium-sized medical practices maintain a strong security posture without the overhead of a full in-house security team.
Example Case: “Bright Smiles Orthodontics”
To illustrate how a medium-sized clinic can approach NIS2 compliance, let’s look at Bright Smiles Orthodontics, a fictional yet realistic example of a growing practice.
6.1 Practice Profile
Ownership & Staffing
- Four partners (all orthodontists)
- 55 employees total (assistants, nurses, front desk, billing, etc.)
Multiple Offices & Digital Systems
- Three clinic locations opened over five years
- Cloud-based patient management for scheduling, billing, and medical records
- IoT-enabled imaging systems that integrate directly with patient files
6.2 Key Challenges
- Limited Internal IT Know-How: The practice relied on a part-time IT contractor for basic troubleshooting. Cybersecurity policies, patching routines, and incident response plans were never clearly defined.
- Rapid Expansion: New offices and telehealth services were launched with minimal standardization. Different tools, configurations, and security practices emerged haphazardly.
- Compliance Blind Spot: With over 50 employees (and growing revenues), Bright Smiles Orthodontics fell under NIS2 requirements. Yet, leadership had only a vague awareness of what the directive entailed.
6.3 Approach & Budget
Concerned about the growing number of healthcare cyberattacks, the partners at Bright Smiles Orthodontics decided to take proactive measures. They engaged an external Cyber-Sicherheitsbeauftragte (similar to a Fractional CISO) to perform an initial security assessment and guide them toward NIS2 compliance. Below is a snapshot of their project timeline, key activities, and associated costs.
Key Activities
Initial Security Assessment & Hardening
- Reviewed all IT infrastructure—cloud-based patient management, imaging devices, and telehealth tools.
- Implemented quick wins (e.g., enabling multi-factor authentication and secure backups).
- Drafted initial policies for access control and incident response, aligned with NIS2 guidelines.
Policy & Governance Establishment
- Created formal governance documents: who’s responsible for reporting incidents, how to handle patching, and vendor security requirements.
- Clarified leadership accountability and ensured board-level buy-in.
- Scheduled annual policy reviews to maintain alignment with evolving threats and regulations.
Staff Awareness & Training
- Conducted an introductory cybersecurity workshop for all staff, from front desk to lead orthodontists.
- Ran phishing simulations to reinforce the importance of cautious email handling.
- Documented training sessions, ensuring compliance with NIS2’s record-keeping expectations.
Ongoing Oversight
- Retained a Fractional CISO two days per month for continuous risk assessment, vendor coordination, and staff training refreshers.
- Deployed monitoring tools for early threat detection, with clear escalation paths for potential breaches.
- Conducted an annual penetration test and comprehensive audit to validate security measures and refine policies.
Positive Outcomes
- Reduced Downtime Risk: With a well-structured incident response plan and tested backups, Bright Smiles Orthodontics dramatically lowered the likelihood of extended outages due to ransomware or other attacks.
- Boost in Patient Trust: Clear communication on data protection and secure telehealth services reassured patients about sharing sensitive information.
- Compliance Confidence: Documented policies, training logs, and a designated Cyber-Sicherheitsbeauftragte provided a strong foundation to meet NIS2 obligations and demonstrate ongoing due diligence.
- Future-Proof Operations: As the practice continues to expand (considering more telehealth options and potentially new locations), cybersecurity has become a routine consideration in every growth decision.
Introducing Sacred Byte & Fractional CISO Services
Navigating NIS2 can be daunting—especially for mid-sized healthcare practices already juggling patient care, staffing, and operational demands. Sacred Byte bridges that gap by delivering cost-effective cybersecurity leadership, ensuring you meet compliance without draining your limited resources.
7.1 Who We Are
Empowering Healthcare Providers Through Cybersecurity
Sacred Byte is a dedicated cybersecurity partner for the healthcare sector. We believe that robust cyber defenses shouldn’t be limited to large hospital networks; every healthcare provider—from a single-location clinic to a multi-site specialty practice—deserves protection. Our mission is to close the gap between complex regulatory requirements and real-world medical operations, letting doctors, nurses, and admin staff concentrate on quality care.
Certified and Experienced in Healthcare IT
Sacred Byte combines deep cybersecurity expertise with hands-on managed IT services for medical practices of all sizes. We hold multiple industry-recognized credentials, including:
- PED Certification (Professional End-User Service Provider)
- KBV Certification (Kassenärztliche Bundesvereinigung, § 390 SGB V)
- Membership in the Alliance for Cybersecurity of the BSI
Real-World Application
Unlike pure consulting firms, we also run internal IT for clients, so our recommendations are battle-tested. From securing telemedicine platforms to streamlining cloud migrations, our end-to-end approach boosts both operational efficiency and regulatory compliance. You can learn more about our services at sacredbyte.com/it-for-medical-practices.
7.2 The Fractional CISO Mode
Part-Time Executive Oversight
Not every clinic needs—or can afford—a full-time Chief Information Security Officer. Our Fractional CISO model brings seasoned cybersecurity leadership on an as-needed basis. We handle:
- NIS2 Compliance Oversight: Mapping requirements to tailored policies and procedures.
- Vendor & IT Management: Coordinating with your providers to maintain robust security standards.
- Staff Training & Phishing Simulations: Fostering a security-conscious culture.
- Incident Response: Guiding containment and official reporting if a breach occurs.
Flexible Engagement for Mid-Sized Clinics
Choose how many days per month of CISO-level support you need, scaling up or down as your practice evolves. Whether revising outdated security policies or conducting annual audits, we help you maintain a strong defense without overextending your resources.
Business Value at a Glance
- Fast-Track Compliance: We leverage our certifications and experience in German healthcare to streamline your path to NIS2 compliance.
- Reduced Financial & Reputational Risk: Proactive threat management and secure systems help prevent expensive breaches and legal liabilities.
- Up-to-Date Threat Intelligence: As active IT service providers, we stay on top of emerging cyber risks so you don’t have to.
- Operational Focus: Offload cybersecurity leadership to us, allowing your staff to concentrate on patient care and operational growth.
In short, Sacred Byte turns regulatory challenges into actionable, value-driven strategies. Our Fractional CISO services deliver enterprise-grade protection at a scale and cost tailored for mid-sized practices—preserving patient trust, enhancing operational efficiency, and ensuring peace of mind.
Timelines & Next Steps
Although NIS2 officially entered into force at the EU level in January 2023, Germany’s transposition into national law has encountered delays. Understanding these shifting deadlines is critical for healthcare providers aiming to stay compliant and protect their patients.
8.1 Key Dates in Germany
17 October 2024: Initial Transposition Deadline
The EU required Member States to adopt NIS2 into national law by this date. Germany missed this deadline—though NIS2 formally repealed the old NIS Directive (NIS1) as of 18 October 2024 .
Late 2024 – Early 2025: First Target
The German cabinet approved a draft “NIS-2 Implementation and Cyber Security Strengthening Act (NIS2UmsuCG)” in July 2024. Initially, the plan was for the law to take effect by January 2025, but legislative delays postponed this timeline.
Spring 2025 (Projected: March)
Currently, the German government aims for the NIS2 law to enter into force in early 2025, likely around March. Political factors could still shift this date further, but Q1/Q2 2025 is the prevailing estimate .
2027–2028: Compliance Milestones
Once the law takes effect, “essential” and “important” entities must self-identify and register with the Federal Office for Information Security (BSI) within three months of being deemed in scope. The most critical institutions (e.g., very large hospitals) must also submit evidence of cybersecurity measures within three years—meaning initial audits for that tier could begin in 2028 .
8.2 Practical Guidance for Healthcare Practices
Don’t Wait on Official Deadlines
Cyber threats aren’t paused by legislative delays. Medium-sized clinics should implement the foundational measures outlined in Chapter 5 — risk assessments, policy creation, staff training, and incident response readiness.
Stay Current with BSI Announcements
The BSI will publish updated criteria and guidelines once Germany finalizes its NIS2 law. Subscribing to bulletins or working with a trusted cybersecurity partner ensures you receive timely notifications.
Prepare for Self-Identification
If you meet the NIS2 thresholds (50+ employees or €10M+ revenue), be ready to register with the BSI once the law is active. Early assessment of your security posture will smooth this process.
Plan for Audits & Evidence
Although the three-year audit window mainly affects the largest “critical infrastructure” providers, any medium-sized practice should maintain thorough documentation of its policies, training sessions, and security controls—key evidence of compliance.
Contact Sacred Byte for Updates
As the law’s final form unfolds, Sacred Byte will keep clients informed on exact requirements and deadlines. By leveraging our Fractional CISO services, you can address the evolving landscape efficiently and without disrupting clinical operations.
By focusing on tangible steps now—and watching for further announcements from the German legislature and the BSI—healthcare providers can ensure they’re well-prepared for the eventual enforcement of NIS2, safeguarding both patient data and regulatory compliance.
Conclusion: Turning Compliance into Resilience
9.1 Why NIS2 Compliance Matters More Than Ever
Healthcare practices face escalating cyber threats that can disrupt everything from billing cycles to life-saving treatments. NIS2 sets a baseline for defending patient data and clinical operations against these attacks, but genuine security requires ongoing vigilance. For mid-sized and larger clinics (over 50 employees or €10 million in annual revenue), the stakes couldn’t be higher:
- Real Consequences: Incidents like the Synnovis ransomware attack highlight the potential for actual patient harm when key systems go offline.
- Regulatory Pressure: Aligning with NIS2 helps avoid fines, legal liabilities, and reputational damage—especially as Germany finalizes its implementation timelines.
- Operational Edge: Proactive cybersecurity isn’t just a mandate; it can also streamline workflows, build patient trust, and ensure uninterrupted quality care.
9.2 Charting Your Path Forward
If you’ve read this far, you recognize that robust security goes beyond a single policy update or software patch. It’s a continuous journey. Here are your next steps:
- Review Your Current Posture: Use the checklist and practical measures in this white paper to gauge where you stand. Identify quick wins—like improving backups or staff training—before tackling more advanced measures.
- Elevate Leadership & Accountability: Consider appointing a Cyber-Sicherheitsbeauftragte or engaging external Fractional CISO services. Empower them to drive regular audits, incident response planning, and policy updates.
- Implement & Document: From risk assessments to incident drills, every improvement should be recorded. Thorough documentation demonstrates compliance and ensures lessons learned are readily accessible.
- Seek Expert Guidance: If you need clarity on specific NIS2 requirements or want to strengthen your cybersecurity strategy without hiring a full-time team, Sacred Byte is ready to help.
How Sacred Byte Supports Your Practice
Consultation & Assessments
Get a thorough, unbiased review of your current security posture, including a roadmap to address NIS2 gaps.
Fractional CISO Services
Receive executive-level security leadership on an as-needed basis, covering compliance, vendor oversight, and staff training.
Tailored Cyber Solutions
From policy creation to monitoring and incident response, we customize solutions around your practice’s unique risk profile and budget.
Ready to secure your practice for the future?
Contact us for a free initial assessment and discover how we can help protect patient care, maintain compliance, and build lasting resilience in an ever-evolving threat landscape.
Appendix
Glossary
- NIS2: Short for the Network and Information Security Directive (EU 2022/2555). An EU-wide legislative framework designed to strengthen cybersecurity for critical and important entities, including healthcare providers.
- BSI (Bundesamt für Sicherheit in der Informationstechnik): Germany’s federal agency responsible for cybersecurity. The BSI issues guidelines, conducts audits, and provides advisories, especially relevant for NIS2 compliance.
- KBV (Kassenärztliche Bundesvereinigung): The National Association of Statutory Health Insurance Physicians in Germany, overseeing outpatient care regulations and IT security guidelines for medical practices.
- Risk Assessment: The process of identifying, evaluating, and prioritizing potential threats to IT systems, data, and processes. Under NIS2, risk assessments form the foundation for targeted security measures.
- Ransomware: A type of malware that encrypts an organization’s files, demanding payment (often in cryptocurrency) to restore access. In healthcare, ransomware can cripple patient care by blocking critical data and services.
- Fractional CISO: A part-time or on-demand Chief Information Security Officer who provides strategic cybersecurity leadership without the full cost or commitment of a full-time executive. Ideal for medium-sized organizations needing specialized expertise.
References
Digital Health. (2024). Synnovis attack led to at least five cases of moderate patient harm. Digital Health. Link
Claims Journal. (2025). Number of affected patients after UnitedHealth cyberattack exceeds one-third of a million. Claims Journal. Link
HIPAA Journal. (2024). Study confirms increase in mortality rate and poorer patient outcomes after cyberattacks. HIPAA Journal. Link
Ponemon Institute. (2022). Cyber Insecurity in Healthcare: The Cost and Impact on Patient Safety and Care. Ponemon Institute. Link
OpenKRITIS. (2024). EU NIS-2 Directive: Impact on German companies. OpenKRITIS. Link
Bundesamt für Sicherheit in der Informationstechnik. (2024). Evaluierung der IT-Sicherheitsrichtlinie in Arztpraxen: BSI-Projekt 598 – SiRiPrax. Bonn: BSI. Link
Bundesamt für Sicherheit in der Informationstechnik. (2024). Cybersicherheit in Arztpraxen: BSI-Studien zeigen dringenden Handlungsbedarf auf. BSI. Link
ENISA – European Union Agency for Cybersecurity. (2024). State of Cybersecurity in the EU: Threats and Incidents. ENISA. Link
European Commission. (2024). NIS-2 Directive: Expansion of Sectors and Requirements. European Commission. Link
European Commission. (2024). NIS-2 Directive: Strengthening Cybersecurity in the EU. European Commission. Link
GUTcert. (2024). NIS2-Umsetzungsgesetz verzögert sich: Inkrafttreten voraussichtlich im März 2025. GUTcert. Link
OpenKRITIS. (2024). EU NIS-2 Directive: Impact on German Companies. OpenKRITIS. Link